Create a SAML Connection
In Kandji, navigate to the Settings page.
Click the Access tab.
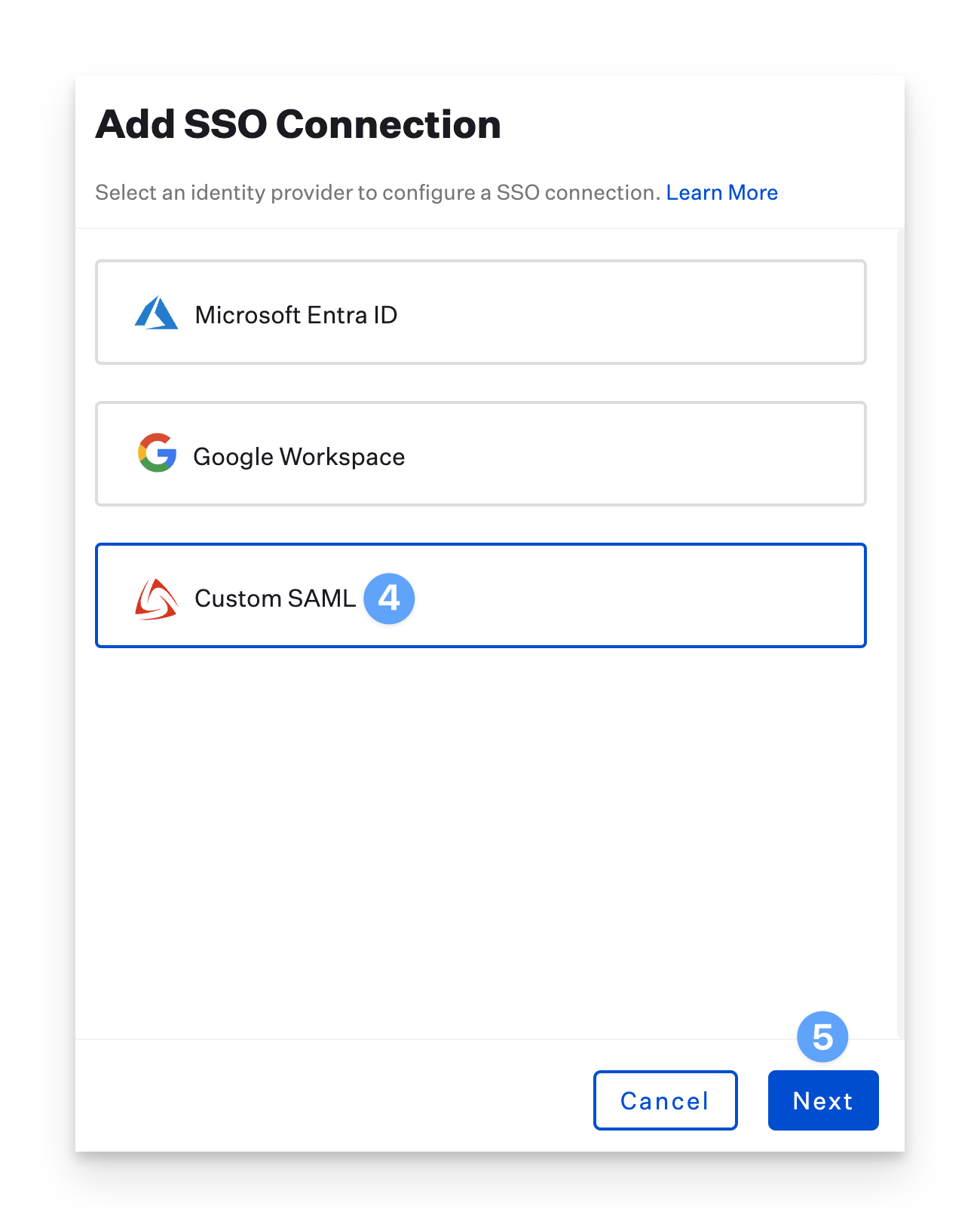
Find the Authentication section and click the Add button at the bottom left of the authentication section.
.png)
In the Add SSO Connection pane, select the Custom SAML option.
Click Next.
Select Show Advanced Details.
Copy the Assertion Consumer Service URL and save it in a text document for later use.
Copy the Entity ID and save it, too.
.png)
Leave this browser tab open as you proceed with the instructions below.
Add the Kandji Application to JumpCloud
Log in to console.jumpcloud.com/login/admin and, in the lefthand navigation bar's User Authentication section, select SSO Applications.
Click on the circular + button, or, if this is your first application, click Get Started.
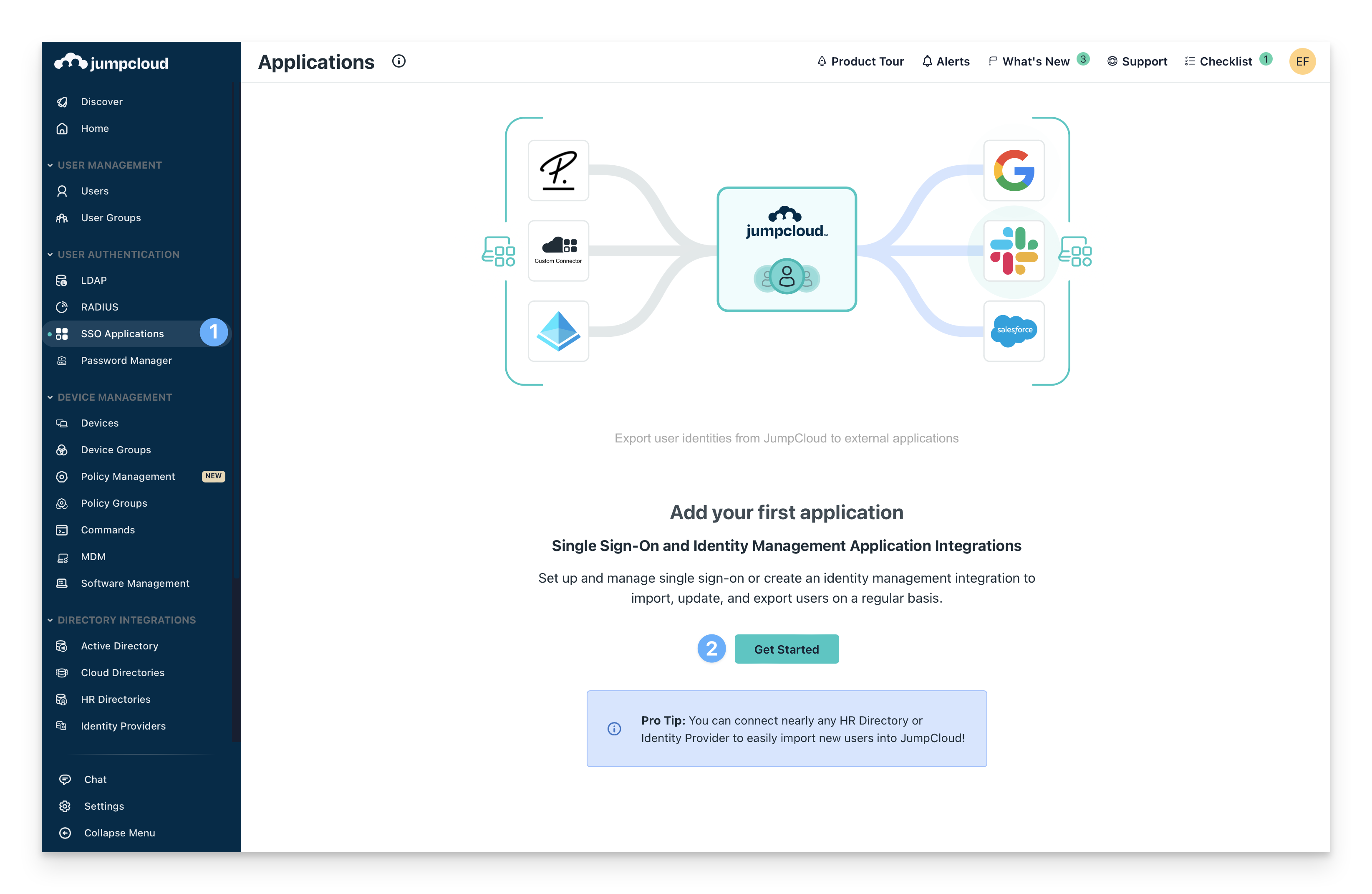
At the bottom of the screen, click Select in the Custom Application tile. Then, click Next.
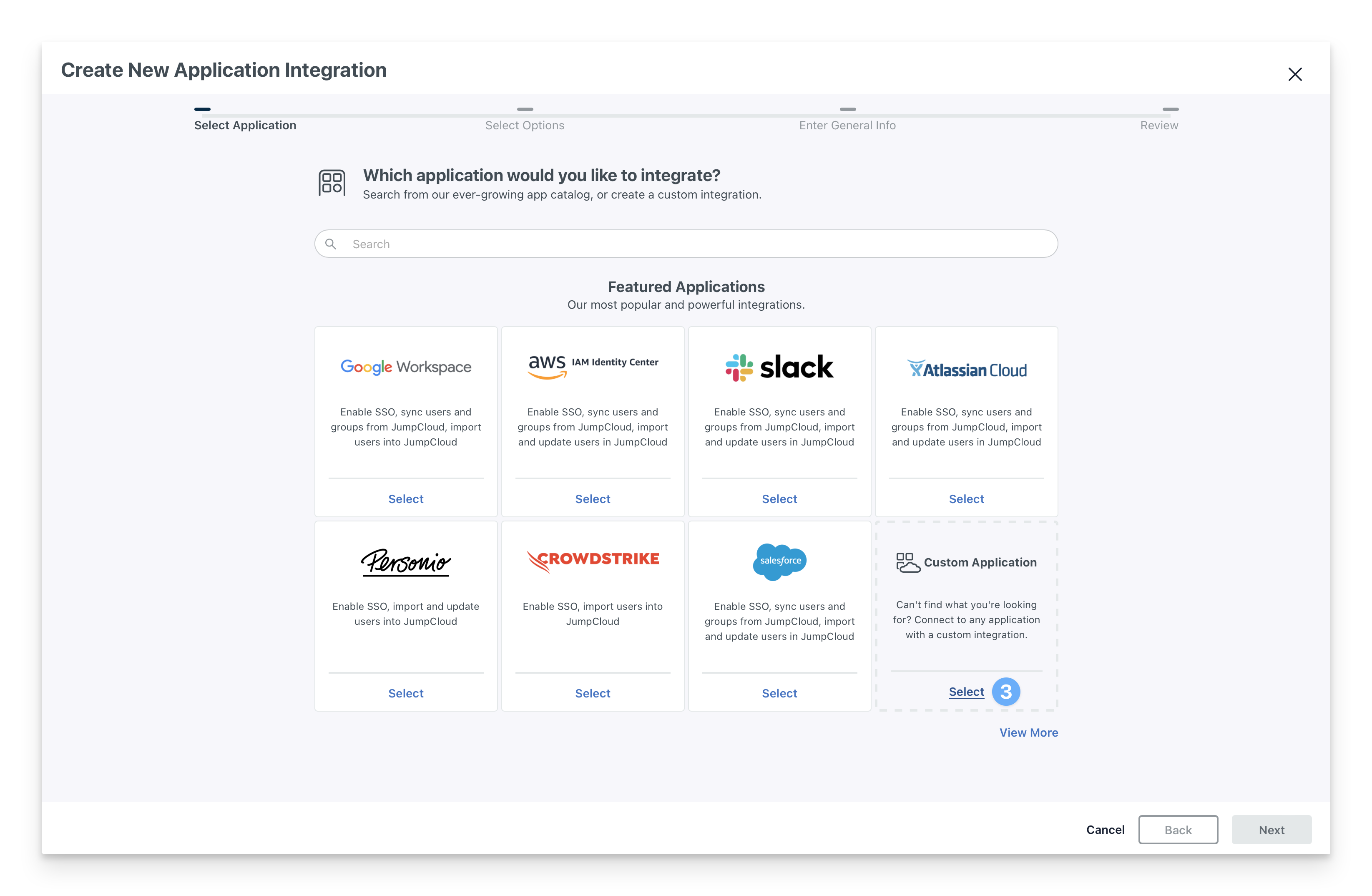
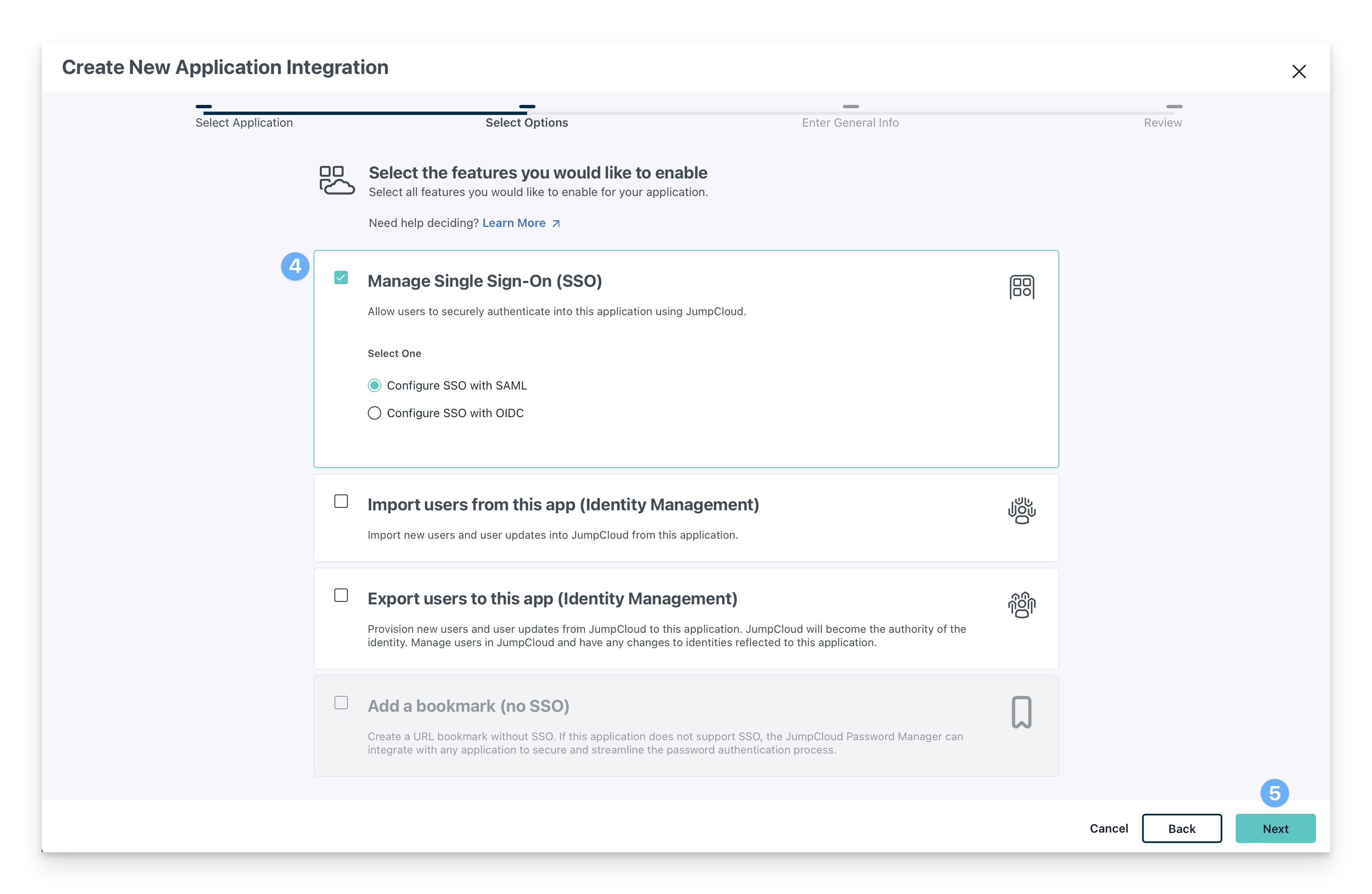
On the Select Options tab, select the following.
Manage Single Sign-On (SSO)
Configure SSO with SAML
Click Next.
On the Enter General Info tab:
Add a name for the Display Label.
Add a Description if desired.
Choose either a color Indicator or upload a logo for the Display Portal Image.
Optionally, choose to show the application in the User Portal.
Expand the disclosure triangle beside Advanced Settings.
In the SSO IdP URL field, enter . The full URL should read https://sso.jumpcloud.com/saml2/kandji
Click Save Application.
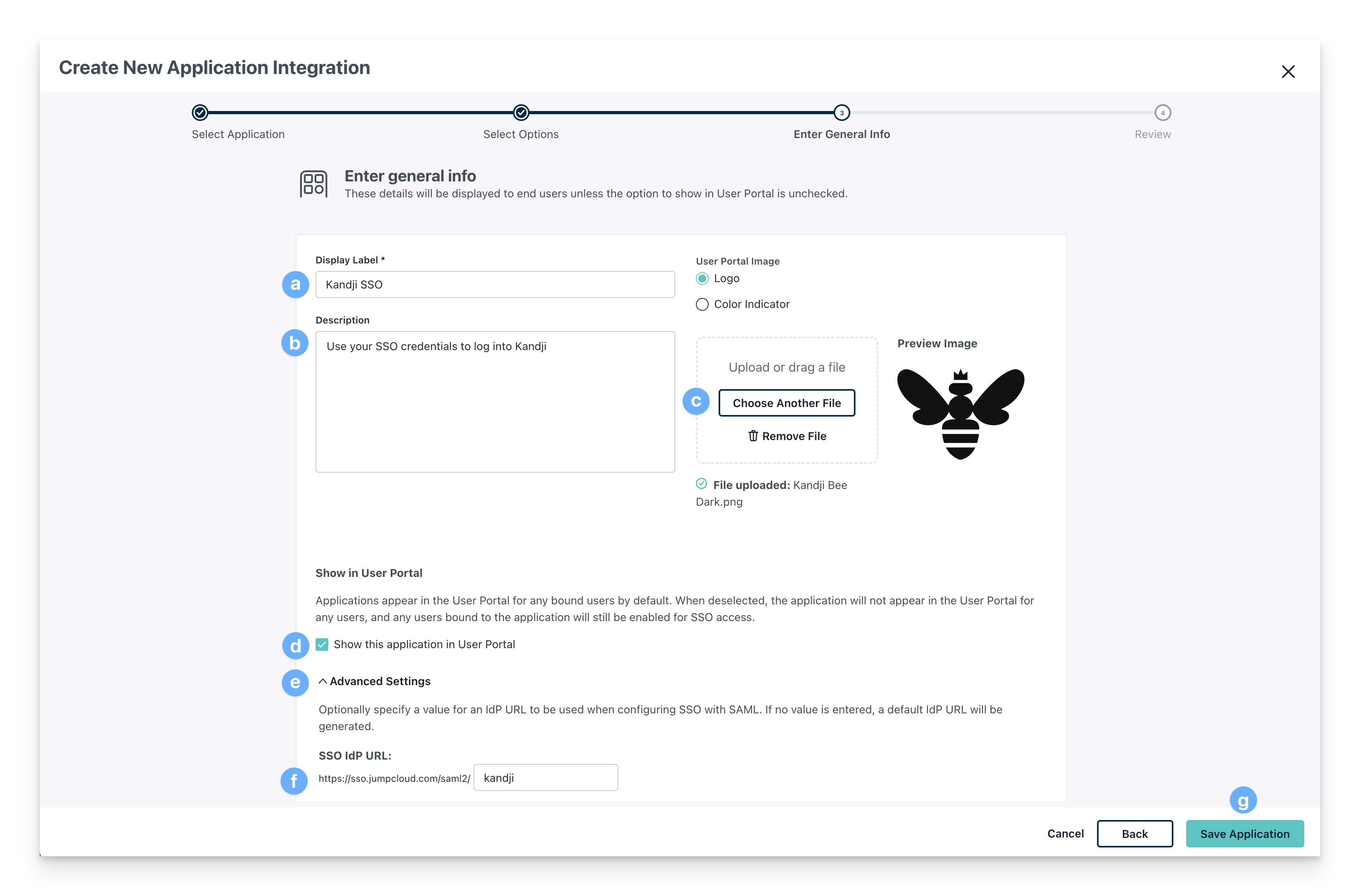
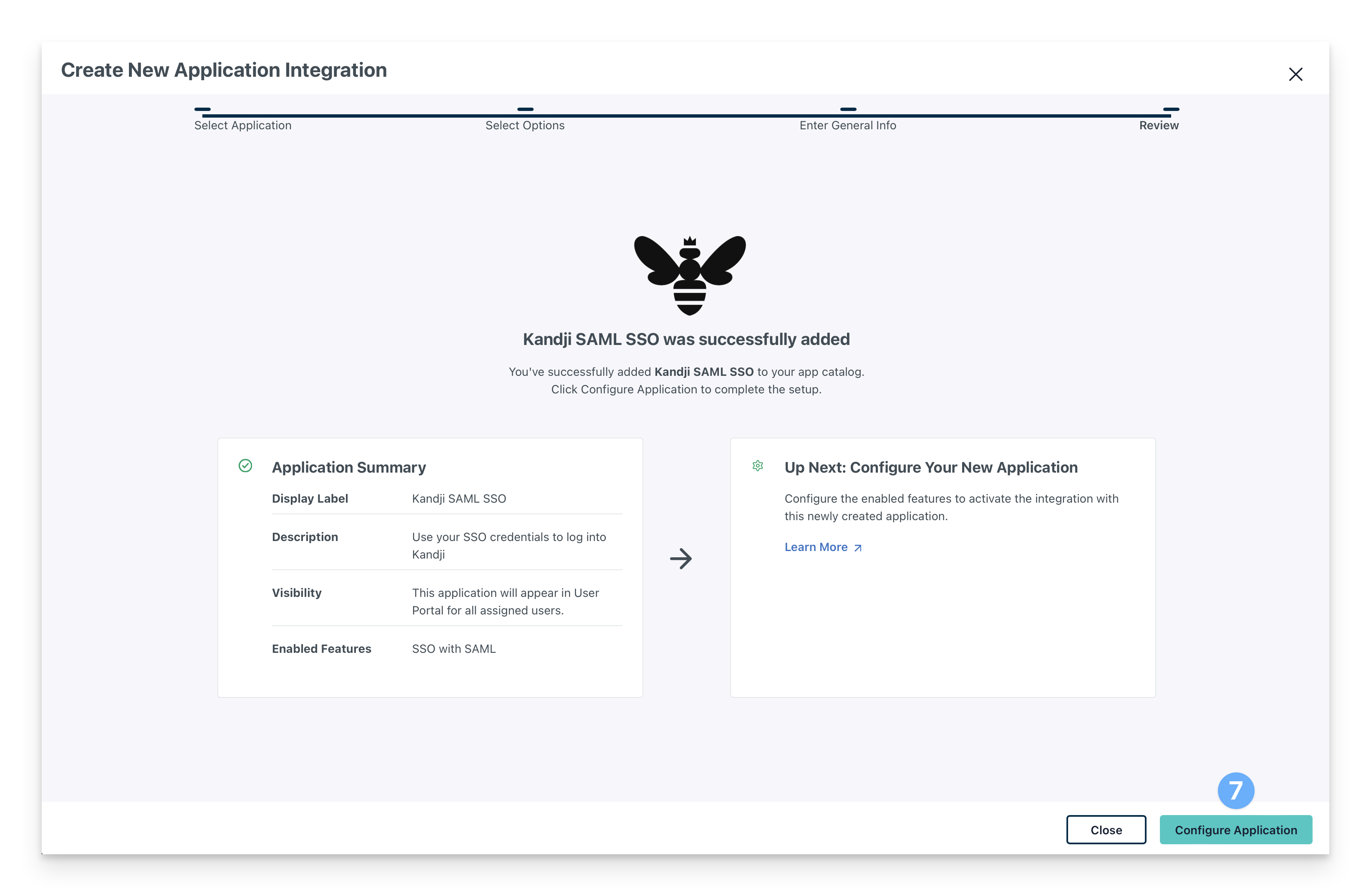
After your application is saved, click Configure Application.
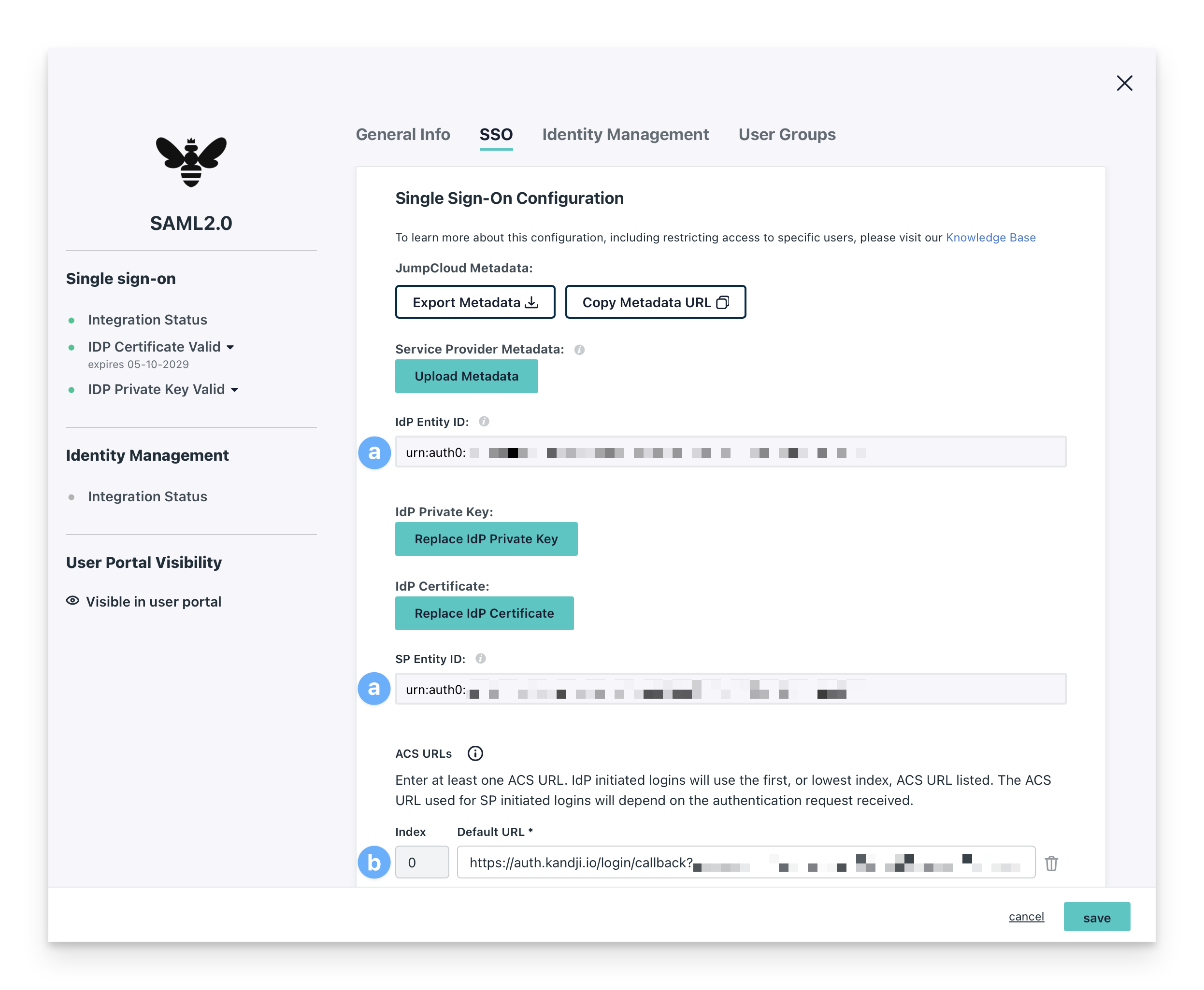
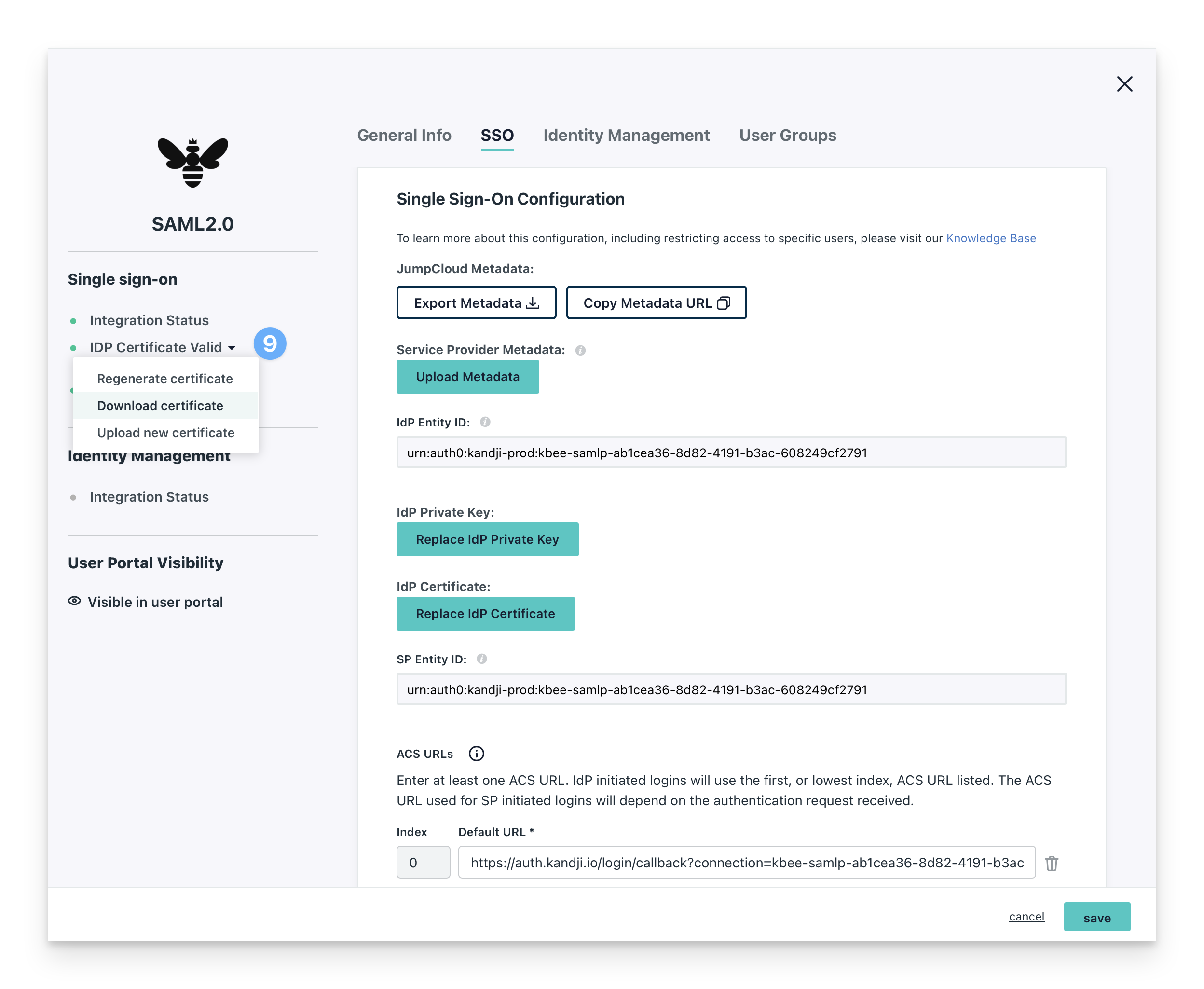
On the SSO tab of the configuration modal:
Copy the Entity ID from Kandji that you saved earlier and paste it into the IdP Entity ID and SP Entity ID fields in JumpCloud.
Copy the Assertion Consumer Service URL from Kandji that you saved earlier and paste it into the ACS URL field.
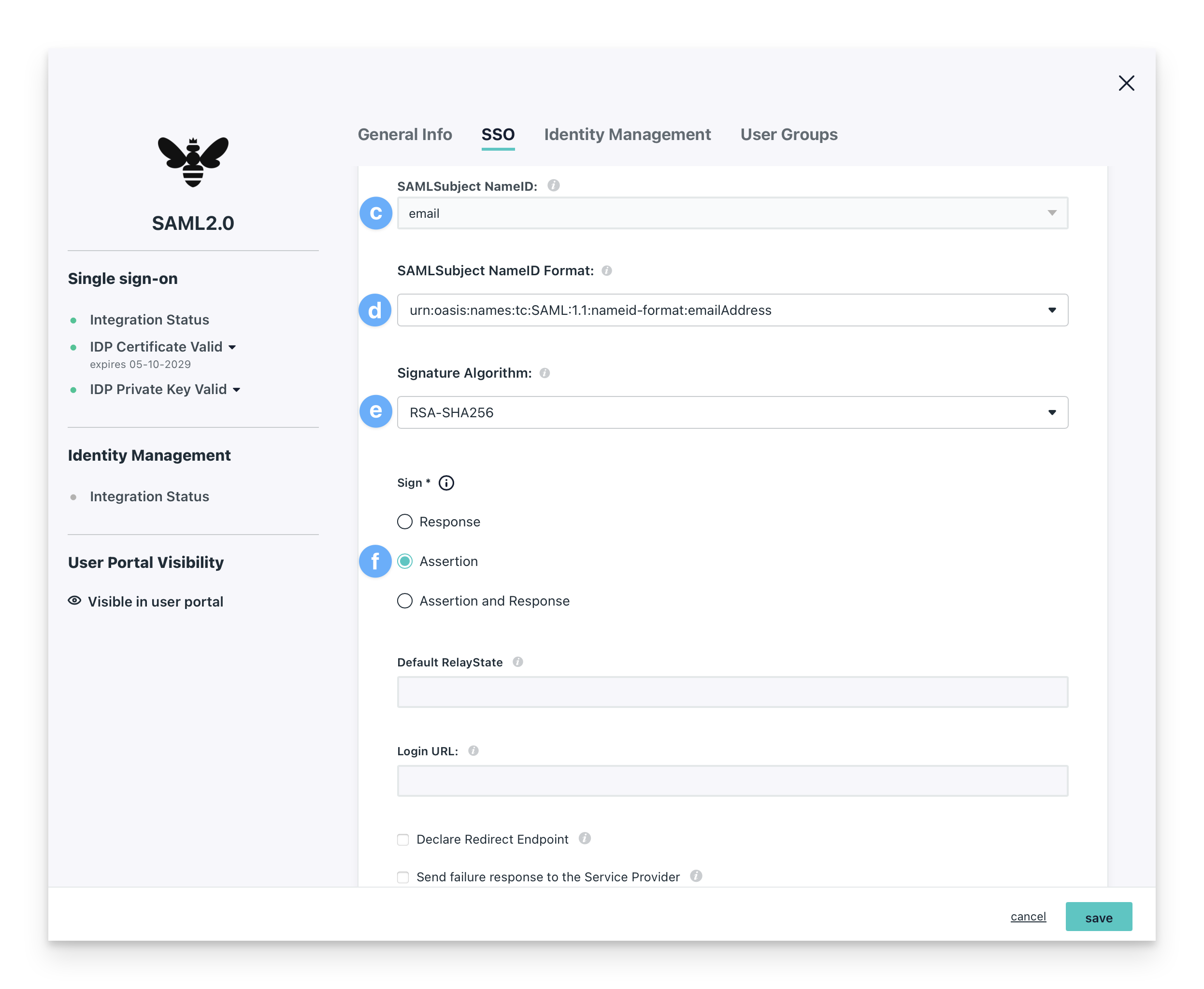
Leave the SAML Subject NameID set to email.
In the SAMLSubject NameID-Format field, select urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress from the dropdown menu.
Set the Signature Algorithm to RSA-SHA256.
Select Sign Assertion.
Ensure the IDP URL is https://sso.jumpcloud.com/saml2/kandji. If it is not, you will need to delete the integration and create a new one. Copy this URL and save it for use in Kandji later.
Click Save.
Once saved, you can go back into the configured application, navigate to the lefthand menu bar of the modal, and click on IdP Certificate Valid. Select Download certificate when presented with the certificate options; it will be used in Kandji later.
On the User Groups tab:
Add a user group to the SSO application. If you want to restrict who can access the SSO app, create another user group in your JumpCloud console and assign it to the SSO app.
Configure the SAML Connection in Kandji
Go back to the Custom SAML modal in Kandji.
Give the connection a Name.
Paste in the Sign-in URL you copied from JumpCloud: https://sso.jumpcloud.com/saml2/kandji.
Upload the certificate you downloaded from JumpCloud.
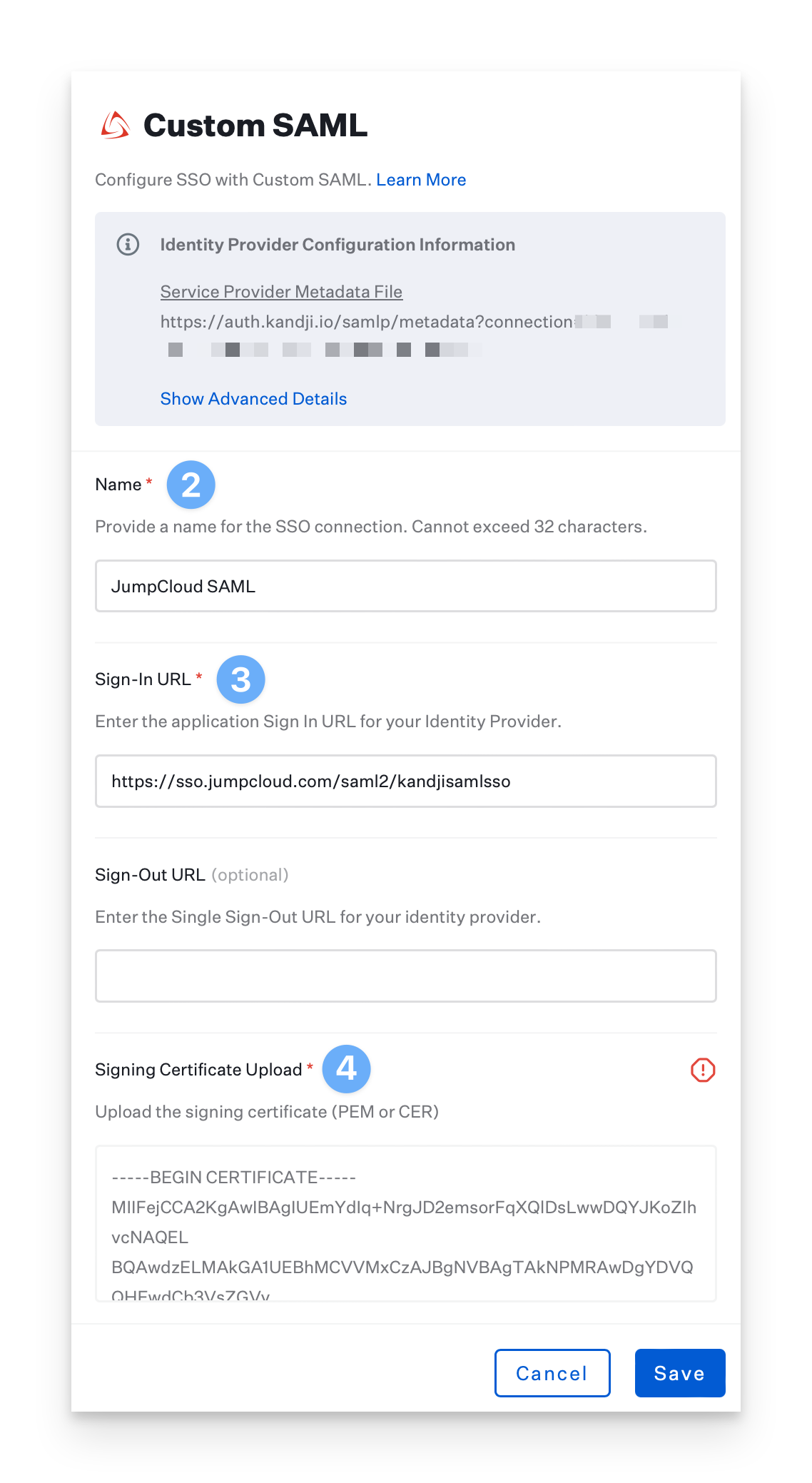
Ensure that the User ID Attribute is set to the default value of:
http://schemas.xmlsoap.org/ws/2005/05/identity/claims/nameidentifierEnsure that Sign Request is set to Yes.
Ensure that Request Algorithm is set to RSA-SHA256.
Ensure that Sign Request Algorithm Digest is set to SHA 256.
Set the Protocol Binding to HTTP-POST.
Click Save and then click Cancel to exit the configuration.
.png)
Enable the SAML Connection
Once you have configured the SAML connection in Kandji and your identity provider, you can enable it. For step-by-step instructions, please refer to the Enable and Manage a Connection section in our Single Sign-on support article.
Enforce Single Sign-on
You can disable the standard authentication connection once you have configured at least one Single Sign-on connection. Disabling Kandji standard authentication will disable the ability for Kandji administrators in your tenant to authenticate via email/password, Google Sign-in, or Office 365 Sign-in. Please refer to our Single Sign-on support article for step-by-step instructions.
Add a User to Kandji
Add a user to the Admin Team in Kandji by clicking New User.
Fill in all of the corresponding user information. This user must exist in JumpCloud and must be assigned to the Kandji SSO app in your JumpCloud tenant.
Click Submit.
.png)
Once the invite is submitted, close the Invite User window.
Refresh the Access page in Kandji. You should see the user you just added.
Check the user’s email to accept the invitation and log into Kandji with the new SAML SSO connection.